What KPIs and Analytics Do Security Intelligence Analysts Use?
Security concerns have grown significantly for companies of all sizes. Nowadays, businesses spend money on effective security measures to safeguard their systems, networks, and data. They must have a thorough awareness of their security posture and dangers in order to do this.
Security intelligence analysts can help in this situation. These experts are in charge of collecting, analyzing, and interpreting data to spot possible risks and weaknesses. They achieve this by using a variety of statistics and key performance indicators (KPIs).
In this post, we'll examine in more detail the KPIs and analytics that security intelligence analysts use to safeguard the information assets of their organizations.
Key Performance Indicators (KPIs) for Security Intelligence Analysts
KPIs are quantifiable metrics that demonstrate how well a company is reaching its objectives. KPIs may assist security teams in evaluating the success of their security strategy and pinpointing opportunities for development in the context of security intelligence analysis. The KPIs that security intelligence analysts use include some of the following:
Threat Intelligence Accuracy
The accuracy of their threat intelligence is one of the major KPIs for security intelligence analysts. This entails calculating the proportion of notifications that are reliable and suitable for action. High levels of precision show that the team is successfully identifying and addressing serious dangers. On the other side, low accuracy levels can mean that the team is spending time and money looking for false positives.
Time to Detect and Respond
Another crucial KPI is the time it takes to identify and address a security event. This indicator aids security teams in gauging how quickly and effectively they are able to counter threats. A quick reaction may lessen the effects of a breach and lower the risk of data loss.
Incident Resolution Time
The length of time it takes to resolve a security event once it has been discovered is measured by incident resolution time. This KPI aids security teams in understanding how soon an issue can be contained and fixed. A security incident's effect may be lessened and the chance of data loss can be decreased with quicker response periods.
False Positive Rate
An alarm that is set off by a lawful action but isn't truly a danger is referred to as a false positive. False positives may waste time and money while diverting security teams' attention from genuine dangers. Security teams may find places where their detection algorithms need to be improved by measuring the false positive rate.
Patch Compliance
For attackers, software flaws are a typical point of access. Any security plan must include patching these vulnerabilities. Security teams may make sure that all devices and systems are updated with the most recent security updates by measuring patch compliance.
Analytics
Security intelligence analysts use a variety of analytics in addition to KPIs to spot possible risks and weaknesses. These are a few of the main analytics they employ:
Log Analysis
Reviewing logs from different systems, including servers, firewalls, and intrusion detection systems, is part of log analysis. The security posture of the company, including any possible weaknesses and suspicious activities, may be better understood with this data.
Network Packet Analysis
Tools for network packet analysis collect and analyze network traffic data in order to spot problems and improve efficiency. Network analysts may immediately discover problems and take remedial action with the help of these tools, which give thorough analysis of network traffic, including the source and destination of data packets, packet timing, and packet size.
Network Traffic Analysis
In order to spot unusual patterns and possible risks, network traffic analysis examines the movement of network traffic. This may include looking at traffic to and from suspect IP addresses or seeing strange network behavior, including the transmission of a lot of data at odd hours.
Threat Hunting
Threat hunting is actively looking for possible dangers that conventional security procedures could have missed. This may include looking for trends in old data or utilizing machine learning techniques to find irregularities in network traffic.
Behavior Analytics
User activity is examined using behavior analytics to spot possible dangers. This can include keeping an eye on user activity for indications of questionable conduct, such trying to access private information or signing in from an odd place.
Vulnerability Assessment
The process of vulnerability assessment include finding and evaluating weaknesses in the organization's systems and applications. This can include running routine scans to find known vulnerabilities or doing penetration tests to find prospective holes.
Threat Intelligence
To detect possible risks, threat intelligence gathers and analyzes data from a variety of sources. This may include keeping an eye on social media, dark web, and open forums for indicators of upcoming assaults. Security teams may spot new risks and modify their security approach by studying this data.

Machine Learning
Algorithms are used in machine learning to evaluate vast volumes of data and spot patterns or abnormalities. This may be especially helpful for spotting possible threats that conventional security procedures might have missed. Machine learning algorithms, for instance, may examine network data to find patterns of activity that could point to an impending assault.
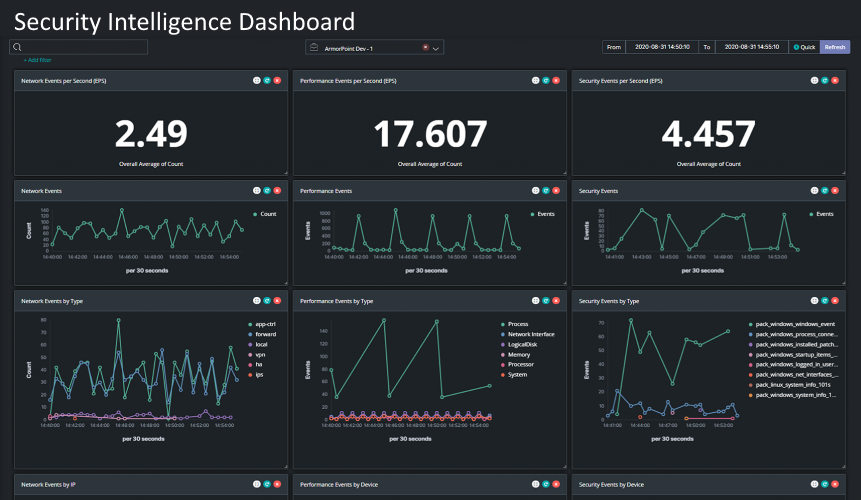
Data Visualization
For the purpose of assisting security teams in spotting patterns and trends, data visualization entails displaying data in a visual manner, such as charts or graphs. This is especially helpful for spotting abnormalities or unexpected behavior that could point to a danger.
Phishing Click Rates
Cybercriminals often employ phishing attempts to steal sensitive data or infect computers with malware. Security teams may find places where staff awareness training may be necessary by tracking how often phishing emails are clicked. High click through rates may be a sign that staff members need more training in spotting phishing scams.
Firewall Effectiveness
A security plan for every firm must include firewalls. Security teams may increase network security and unwanted traffic blocking by measuring the firewall's efficacy. By examining traffic logs and detecting any unlawful traffic that has passed through, one may assess the efficacy of a firewall.
Password Policy Compliance
Organizations often face a security risk from using weak passwords. Security teams may assist guarantee that workers are using strong passwords and adhering to best practices for password management by monitoring compliance with the password policy. This might include calculating the proportion of workers who have changed their password within a certain period or the proportion of passwords that match complexity standards.
User Training Completion Rates
Training for employee awareness is a crucial component of every organization's security plan. Security teams may make sure that all staff members are getting the essential training to identify and react to possible threats by monitoring user training completion rates. The number of workers who complete the training program or the proportion of employees who finish the training within a certain period may be used to calculate completion rates.